We discovered today, two years after canceling hosting services with Kualo that our old website is still live and publicly accessible. While we are pointing out a specific occurrence involving Kualo, we wish it to serve as a warning that could easily apply to any web hosting provider. We would stress that we were very happy with Kualo when hosting with them.
The implications of such an event may be severe, especially when the website contains confidential data, such as customer delivery addresses, or worse credit card data.
What makes this more dangerous, is that software needs to be regularly updated to keep it secure. Where you have older versions of websites that still may be accessible via IP versions of the URL, the chance they will be compromised is so much greater.
Timeline of Events
To understand the situation it is useful to take you through the events as they happened:
November 2011 - Hosting Purchased
We initially chose Kualo back in November 2011 as they had an excellent reputation, and being relatively new to web hosting at that time we wanted to go with a company that was known for providing excellent support. We signed up for two years to get a good deal. The website was for a project to provide basic web design, hosting and SEO services for a small number of clients, hence the need for a Reseller Plan. We used WHMCS for our billing platform, and as such (and this stresses the seriousness of this matter) a small number of basic client details were stored on the server.

November 2013 - Hosting Canceled
By the end of November 2013, we had already moved our website to another provider. We were moving on to different projects (i.e., away from client SEO, and on to writing about SEO and Web Hosting (the first versions of this website)), and wanted to have more flexibility that a VPS had to offer. We decided at that time to use Hostnine (which we recommended for a long time until EIG took them over).
Having canceled the service, we moved on, and for some time, forgot all about Kualo (although we still had a couple of domains with them at this particular point in time).
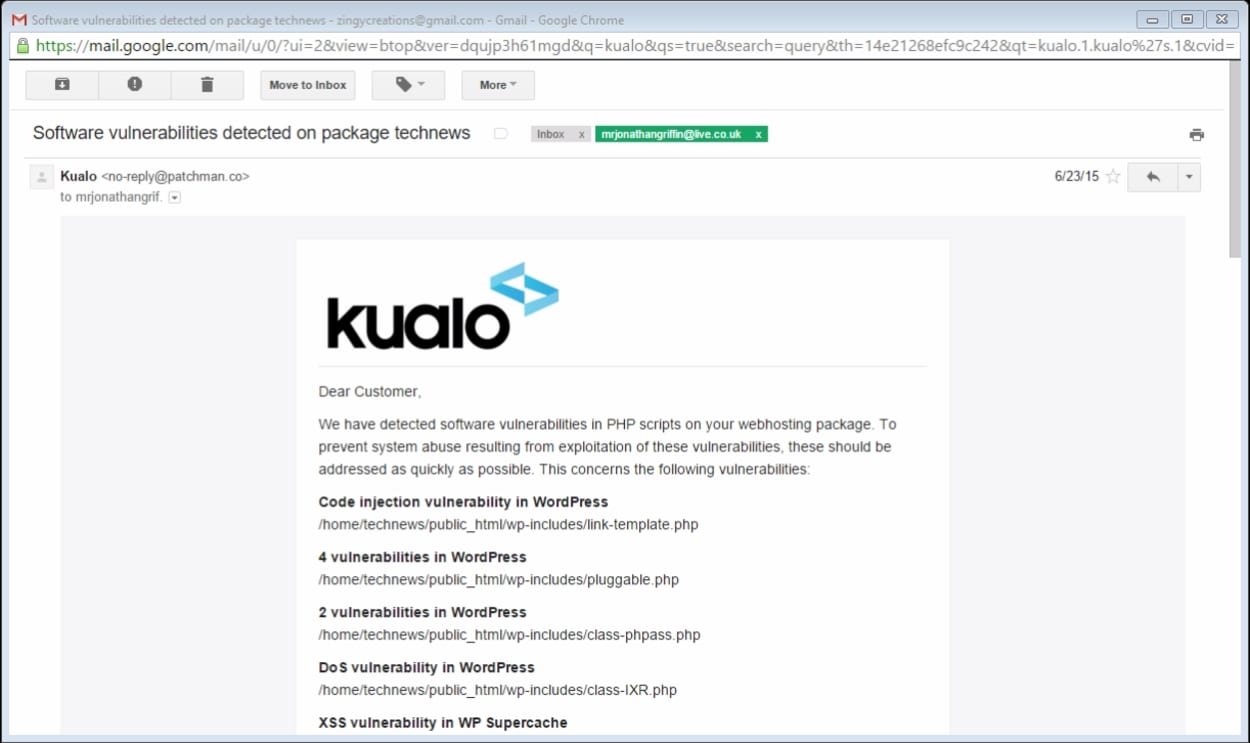
23rd June 2015 - Software Vulnerabilities Detected Notifications
It came as a bit of a surprise when nearly two years later we got some notifications from Kualo about software vulnerabilities in software installed on their services. Looking at the email, Kualo seems to have employed a third party service (Patchman) which scans their servers looking for out of date software, and then notification their users of the same.
As you will see below, the account was now around two years old, with significantly out of date software. Quite a few vulnerabilities were picked up, and this was just one email of around half a dozen or so we received about different cPanel accounts (we had a reseller account). The risk of a data breach \ data being stolen was real.
23rd June 2015 - Issue Raised in a Ticket
Obviously, the first thing you do when such an incident occurs is to reach out and query why the data is still there:

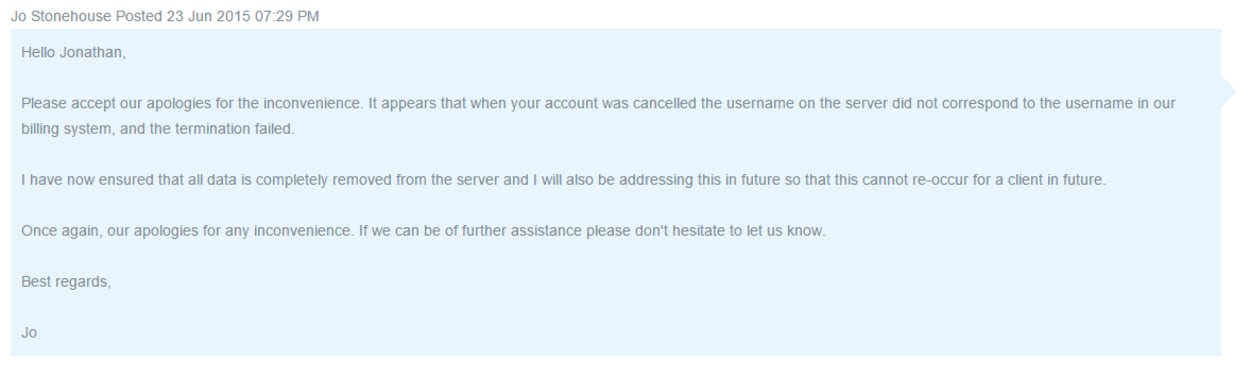
23rd June 2015 - Response from Kualo
Great, within just 15 minutes we got a response from Kualo with a resolution. Apparently, the username within their account system did not correspond with the user name on the hosting account, and as such the termination of the account failed.
Kualo uses one of the most popular billing and automation systems called WHMCS. We are surprised there are no safeguards in place that would pick this up. We have reached out to them for comment.
Great, so with the problem resolved, we accepted this was a one-off and just forgot about it.
Present - Bots still trying to register on a website on the deleted account
We are receiving emails about users registering on the websites that should have been deleted when the hosting expired. We have many these emails, and we can’t say for certain how long they have been coming for (we should check our spam folder more regularly).
As we received explicit confirmation that that websites \ old data had been deleted, and it being nearly two years since, we are concerned. Why is the account still there?
You can see an extract of one of the email messages received below:

Clearly, this is getting more serious. The website is still accessible by the public, bots, and hackers, presumably via the IP version of the address. This issue clearly needs addressing, and we have reached out to Kualo.
Kualo Responds
Kualo was very helpful investigating the issue, and it would seem that the problem was caused by allowing one of my websites for my account on a different server. Indeed, recalling the initial setup (that we had totally forgotten about until recently reminded), they were extremely helpful in assisting with a unique configuration. In the response, Kualo made a detailed reply to me personally about how the incident happened, and although we won’t reproduce it here, they sent us screenshots of the processes \ checklists they have implemented to ensure us that this will not happen again.
The biggest concern for us is the indication that this issue could be widespread. Because the WHMCS system does not provide a notification when deletions fail, web hosts could have many “orphaned” accounts on their system that they do not know exist. Kualo has submitted a feature request to deal specifically with this problem, but it remains to be seen whether this will be implemented.
Here is their response in full:
“After Jonathan made us aware of the fact that his account was not properly removed from the server after cancellation, we immediately rectified this by terminating the reseller account. The issue originally occurred due to a username mismatch between the server username, and the username in WHMCS itself. This mismatch occurred due to human error following a server transfer and username change - the member of our team who handled this transfer did not update WHMCS with the revised username, which then prevented WHMCS from properly terminating the account upon cancellation. After Jonathan informed us of this, we additionally put measures in place to ensure that all the usernames in WHMCS properly match with the server usernames. We have also adjusted our process for server transfers and username changes to ensure that our team document that all steps have properly been followed each time such changes are requested by a customer.
The account had an A-typical setup, where the main domain was hosted on a separate server to the resold accounts itself. When the resold accounts were terminated after Jonathan initially raised this with us, we unfortunately missed the fact that his main account resided on a different server. Upon receipt of his email today, we have also rectified this issue, and are presently putting further measures in place to ensure that there can be no similar issues in future.
Kualo takes the protection of client data very seriously, and the measures we have now put in place aim to ensure that such issues do not reoccur. These issues however may unfortunately be widespread amongst hosts who use WHMCS, and whilst measures can and should be put in place by the host to avoid such scenarios, we would additionally welcome further safeguards to be built into the WHMCS software. In the same way that WHMCS notifies hosts when automatic account creation fails, we would welcome changes that sends a notification where auto termination does not complete successfully. We appreciate that WHMCS and cPanel are working on a much deeper integration, and a more integrated audit functionality to help identify and alert hosts to orphaned accounts is very much essential. We have made these suggestions to WHMCS via their requests system, and we hope that they will be discussed and implemented in future releases.
We would like to reassure our customers and readers that the measures we have put in place mean that there are no other such incidents on our servers, and that our new processes will also help ensure that similar discrepancies do not occur in future.”
We have forwarded a copy of this response to WHMCS for comment.
So how do you ensure that your data is deleted?
That is a good question. Obviously asking your host to check specifically is the most obvious method, but in our case, we received those assurances.
What we recommend is that you ensure that before canceling your hosting account, you specifically remove all files, databases and emails yourself to ensure they are gone. You should not rely on your hosting provider to do this if your data contains confidential information.
Final Thoughts
This story is more about the possibility that many hosting providers may have unknowingly not deleted old data \ accounts off their servers. We have specifically mentioned the WHMCS automation system, but it could apply to one of a number of billing \ automation systems.
There could be many “orphaned” accounts containing extremely confidential data that is vulnerable to attack, and as such something that needs to be addressed.
We are very satisfied with the response by Kualo, but not all hosting providers are as diligent or well organized as them. This makes us worry, and something that companies such as WHMCS, and also the web hosting providers themselves need to address urgently.
